United States, United Kingdom, and Australia Jointly Target Russian Cybercrime Infrastructure: Media Land and Aeza Group
On November 19, 2025, the U.S. Department of the Treasury’s Office of Foreign Assets Control (OFAC), Australia’s Department of Foreign Affairs and Trade (DFAT), and the United Kingdom’s Foreign, Commonwealth & Development Office (FCDO) jointly announced a new round of sanctions against multiple Russia-based bulletproof hosting (BPH) providers and associated individuals, citing their support for cybercrime activities, including ransomware operations. The primary targets of this action include key leaders and affiliated entities of Media Land, as well as core members of Aeza Group and related shell companies.

What is a “bulletproof hosting” provider ?
Bulletproof hosting providers are a type of internet infrastructure service specifically catering to cybercriminals. By leasing virtual or physical servers, they host illicit content and support various forms of malicious activity. The term “bulletproof” is essentially a marketing label; these services are not truly impervious to law enforcement. Instead, their operators deliberately refuse to comply with takedown requests, systematically ignore abuse reports and content removal notices, and create an environment in which their infrastructure is extremely difficult to dismantle directly. Within this high-tolerance environment, cybercriminals can communicate, operate forums and illicit websites, deliver malware and phishing campaigns, and run money-laundering operations without fear that their services will be terminated due to law enforcement intervention. As a result, bulletproof hosting providers hold a critically important position in the global cybercrime ecosystem — both difficult to disrupt and deeply influential in enabling the scale and persistence of malicious activity.
Sanctions Details
Media Land: A bulletproof hosting network led by Volosovik
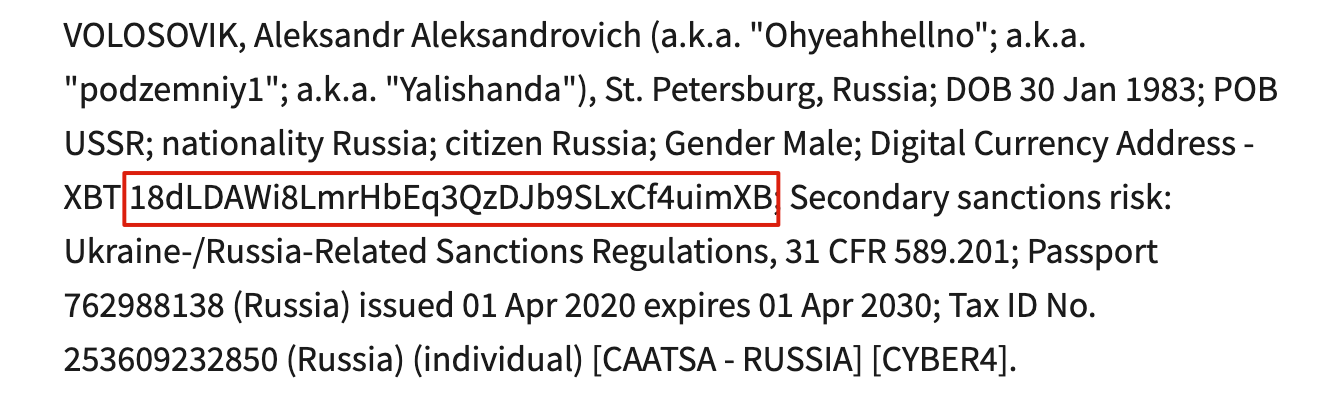
Media Land LLC (Media Land), headquartered in St. Petersburg, Russia, is a typical bulletproof hosting (BPH) provider that has long supplied dedicated servers and infrastructure to ransomware groups such as LockBit, BlackSuit, and Play, while also supporting multiple large-scale DDoS attacks. Its key figure, Aleksandr Volosovik (a.k.a. “Ohyeahhellno,” “podzemniy1,” “Yalishanda”), has been active on underground forums since 2010 and maintains close ties with several major cybercriminal gangs, including Evil Corp, LockBit, and Black Basta. Under Volosovik’s leadership, Media Land has built a hosting ecosystem that covers several critical stages of the cyberattack chain, providing stable infrastructure for underground exchanges, money-laundering services, fraud groups, hackers, and ransomware operators.
According to the U.S. Department of the Treasury, Media Land was designated for sanctions due to its direct or indirect involvement in, or support to persons located outside the United States engaging in, malicious cyber activities that have threatened — or could threaten — the national security, foreign policy, economic health, or financial stability of the United States. These activities typically aim to disrupt the availability of computers or networks, or to compromise the integrity of information stored on them.
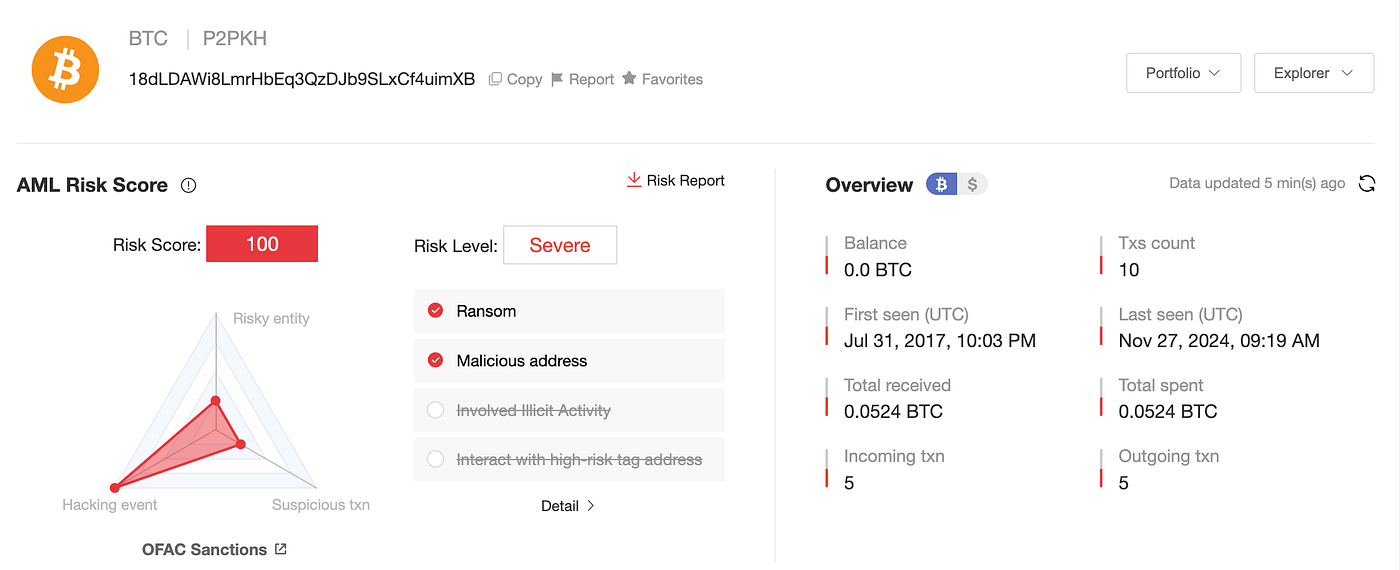
As part of this sanctions action, a Bitcoin address directly controlled by Aleksandr Volosovik has also been added to the OFAC sanctions list:
According to MistTrack, the anti–money laundering tracking and analysis system developed by SlowMist, the Bitcoin address has remained active from August 2017 to November 2024, during which it received a total of five incoming transactions amounting to 0.0524 BTC.
The U.K. noted that malicious infrastructure supported by entities such as Media Land poses a significant threat to national security. Official data shows that cyberattacks caused losses of up to £14.7 billion to U.K. businesses in 2024 — equivalent to 0.5% of the country’s GDP — and the figure continues to rise each year.
The sanctioned entities associated with Media Land in this action include:
1. Individuals (3 persons):
Aleksandr Volosovik (Volosovik): General Manager of Media Land. Under the alias “Yalishanda,” he promoted Media Land’s illicit services on cybercrime forums and provided servers and troubleshooting support for ransomware operators and DDoS attackers.
Kirill Zatolokin (Zatolokin): An employee of Media Land responsible for collecting payments from clients and coordinating with other cybercriminal actors. He worked closely with Volosovik to manage Media Land’s overall operations.
Yulia Pankova (Pankova): An employee of Media Land who was aware of Volosovik’s criminal activities and assisted him in handling legal matters and financial affairs.
2. Companies (3 entities):
ML Cloud: A sister company of Media Land. Its technical infrastructure is frequently used jointly with Media Land to support ransomware operations and DDoS attacks.
Media Land Technology (MLT) and Data Center Kirishi (DC Kirishi): Wholly owned subsidiaries of Media Land. They were designated by OFAC due to being controlled by Media Land or acting on its behalf.
Aeza Group: Covert Expansion Following Sanctions
Aeza Group (Aeza) is also headquartered in St. Petersburg, Russia, and centers its operations around bulletproof hosting services. It has long provided infrastructure support to ransomware and information-stealer groups such as Meduza, Lumma, BianLian, and RedLine, and has hosted the Russian dark-web drug marketplace BlackSprut, making it a critical infrastructure hub within the cybercrime ecosystem. Because Aeza’s services were used to facilitate attacks targeting the U.S. Defense Industrial Base, technology companies, and victims worldwide, the U.S. Department of the Treasury’s Office of Foreign Assets Control (OFAC) designated Aeza and its affiliated entities for sanctions in July 2025.
After being sanctioned, Aeza did not cease operations. Instead, it initiated a series of covert expansion and evasion measures. Its leadership registered new shell companies, rebranded its services, established offshore front companies, and migrated its IP infrastructure in an effort to obscure actual ownership and evade regulatory tracking. Several of these newly created entities continued providing hosting support for similar malicious activities, supplying infrastructure for ransomware groups, information-stealer operators, and dark-web marketplaces.
In this round of sanctions, the United States, United Kingdom, and Australia explicitly targeted Aeza’s evasion network, designating key individuals and front entities involved in its operations and sanction-evasion efforts. These include:
1. Individuals (2 persons):
Maksim Vladimirovich Makarov (Makarov): Aeza’s new executive, responsible for making key decisions to advance Aeza’s sanction-evasion activities.
Ilya Vladislavovich Zakirov (Zakirov): Assisted in establishing new companies and payment channels to conceal Aeza’s ongoing operations.
2. Companies (3 entities):
Hypercore Ltd. (Hypercore): A U.K.-based front company created by Aeza Group, used to migrate IP infrastructure and circumvent sanctions.
Smart Digital Ideas DOO (Smart Digital) and Datavice MCHJ (Datavice): Companies in Serbia and Uzbekistan, respectively, used by Aeza to evade sanctions and build technical infrastructure with no publicly visible links to the Aeza brand.
Summary and Recommendations
The joint sanctions imposed by the United States, United Kingdom, and Australia send a clear message: as global cooperation against ransomware and high-risk cybercrime continues to deepen, law enforcement efforts are increasingly shifting from targeting individual attackers to focusing on the critical infrastructure that enables their operations. The bulletproof hosting services provided by Media Land, Aeza Group, and their affiliated entities serve as hidden pillars supporting a wide range of persistent cybercriminal activities. As sanction coverage expands, enterprises and institutions must strengthen their compliance frameworks to avoid exposure to sanctioned infrastructure, tainted funds, or associated entities that could introduce additional operational and legal risks.
In practice, on-chain risk monitoring and compliance management have become essential components of modern security operations. Through technical measures, organizations can conduct real-time screening of transaction addresses, fund sources, and linked entities to achieve proactive risk mitigation. Built on years of blockchain security research and risk-control expertise, SlowMist’s anti–money laundering tracking and analysis system, MistTrack, provides stable, reliable on-chain risk-control capabilities and robust AML compliance solutions for exchanges and businesses, while also offering precise data analysis, real-time risk monitoring, and comprehensive compliance support for individual users, enterprise teams, and developers.
MistTrack enables users to:
- Identify fund sources and detect whether they originate from sanctioned wallets or high-risk addresses, preventing the acceptance of tainted assets.
- Conduct pre-transaction address screening to avoid interactions with sanctioned or suspicious funds, thereby reducing the risk of asset freezes.
Currently, MistTrack has accumulated over 400 million address labels, 1,000+ entities, 500,000+ threat intelligence data points, and 90 million+ high-risk addresses, providing strong support for digital asset security and anti–money laundering efforts.For additional insights into practical on-chain AML methodologies, refer to the case study: “Case Study: MistTrack Empowers Virtual Asset Funds to Achieve AML Compliance and Risk Control.”For more information, please visit https://aml.slowmist.com.
Related links:
https://home.treasury.gov/news/press-releases/sb0319
https://www.cyber.gov.au/sites/default/files/2025-01/Bulletproof-hosting-providers.pdf
About SlowMist
SlowMist is a threat intelligence firm focused on blockchain security, established in January 2018. The firm was started by a team with over ten years of network security experience to become a global force. Our goal is to make the blockchain ecosystem as secure as possible for everyone. We are now a renowned international blockchain security firm that has worked on various well-known projects such as HashKey Exchange, OSL, MEEX, BGE, BTCBOX, Bitget, BHEX.SG, OKX, Binance, HTX, Amber Group, Crypto.com, etc.
SlowMist offers a variety of services that include but are not limited to security audits, threat information, defense deployment, security consultants, and other security-related services. We also offer AML (Anti-money laundering) software, MistEye (Security Monitoring), SlowMist Hacked (Crypto hack archives), FireWall.x (Smart contract firewall) and other SaaS products. We have partnerships with domestic and international firms such as Akamai, BitDefender, RC², TianJi Partners, IPIP, etc. Our extensive work in cryptocurrency crime investigations has been cited by international organizations and government bodies, including the United Nations Security Council and the United Nations Office on Drugs and Crime.
By delivering a comprehensive security solution customized to individual projects, we can identify risks and prevent them from occurring. Our team was able to find and publish several high-risk blockchain security flaws. By doing so, we could spread awareness and raise the security standards in the blockchain ecosystem.



