2025 Blockchain Security and AML Annual Report

Due to space limitations, this article only presents the key points from the analysis report. The full content can be downloaded via the PDF link at the end.
I. Overview
In 2025, the blockchain industry continued to evolve rapidly, with the combination of macroeconomic conditions, regulatory uncertainties, and intensified attack activity making the overall security landscape significantly more complex. Specifically, hacker groups and underground criminal networks have become highly professionalized, with North Korea–linked hackers frequently active. Information-stealing malware, private key hijacking, and social engineering phishing emerged as primary attack methods. Additionally, DeFi permission management and Meme token issuance repeatedly led to substantial losses. The service-oriented models of RaaS (Ransomware-as-a-Service) and MaaS (Malware-as-a-Service) have lowered the barrier to entry for cybercrime, enabling attackers without technical backgrounds to execute attacks rapidly. Meanwhile, underground money laundering systems have continued to mature, with Southeast Asian scam clusters, privacy tools, and mixing services forming multi-tiered fund flows.
On the regulatory front, countries accelerated the implementation of AML/CFT frameworks, and multiple cross-border enforcement actions improved on-chain tracking and asset freezing efficiency. Regulation is gradually shifting from isolated interventions to systematic containment, while the legal boundaries for privacy protocols are being redefined to better distinguish between technical features and criminal use.
Against this backdrop, this report provides an in-depth analysis of typical blockchain security incidents and attack techniques in 2025, trends in APT organization activities, the evolution of money laundering models, and global regulatory enforcement developments. We aim for this report to serve as a timely, structured, and insightful reference for industry practitioners, security researchers, and risk compliance officers, enhancing their ability to identify, respond to, and anticipate risks.
II. Blockchain Security Trends
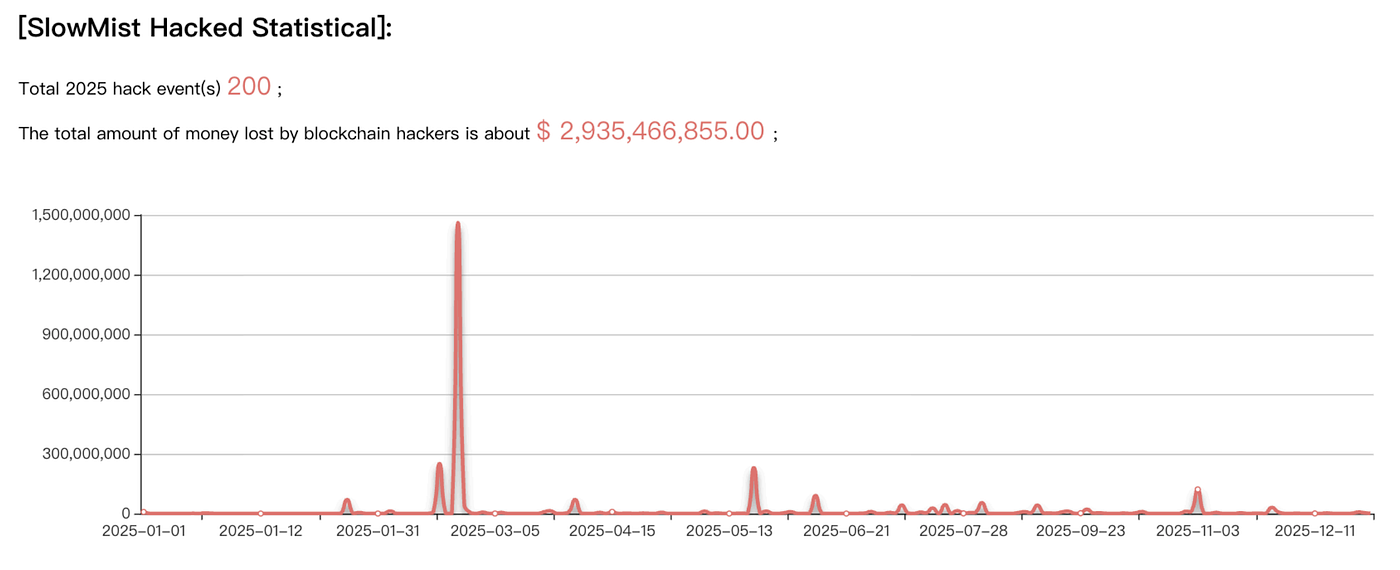
According to incomplete statistics from SlowMist Hacked, a blockchain security incident archive maintained by SlowMist, a total of 200 security incidents occurred during the year, resulting in approximately $2.935 billion in losses. In comparison, 2024 saw 410 incidents with around $2.013 billion in losses. While the number of incidents declined year-over-year, the total amount of losses increased by approximately 46%.
(Note: The data in this report is based on token prices at the time of each incident. Due to price fluctuations, unreported cases, and the exclusion of individual user losses, the actual amount of losses is likely higher than the figures presented.)
Overview of Blockchain Security Incidents
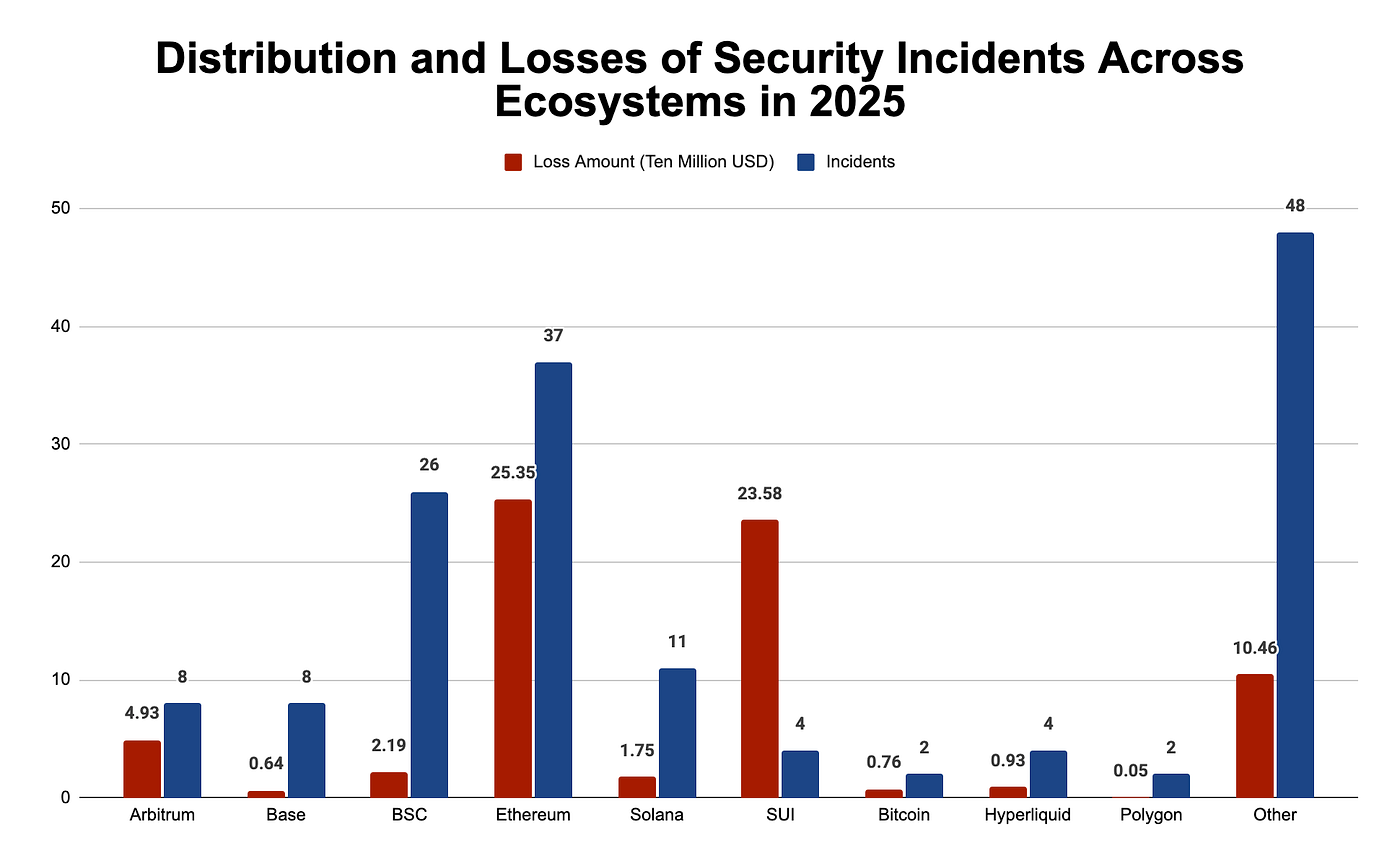
From an ecosystem distribution perspective, Ethereum remains the most frequently attacked and suffers the largest losses, with total losses of approximately USD 254 million for the year, significantly ahead of others. BSC follows closely, with related losses of around USD 21.93 million, while Solana ranks third, with annual losses of approximately USD 17.45 million.
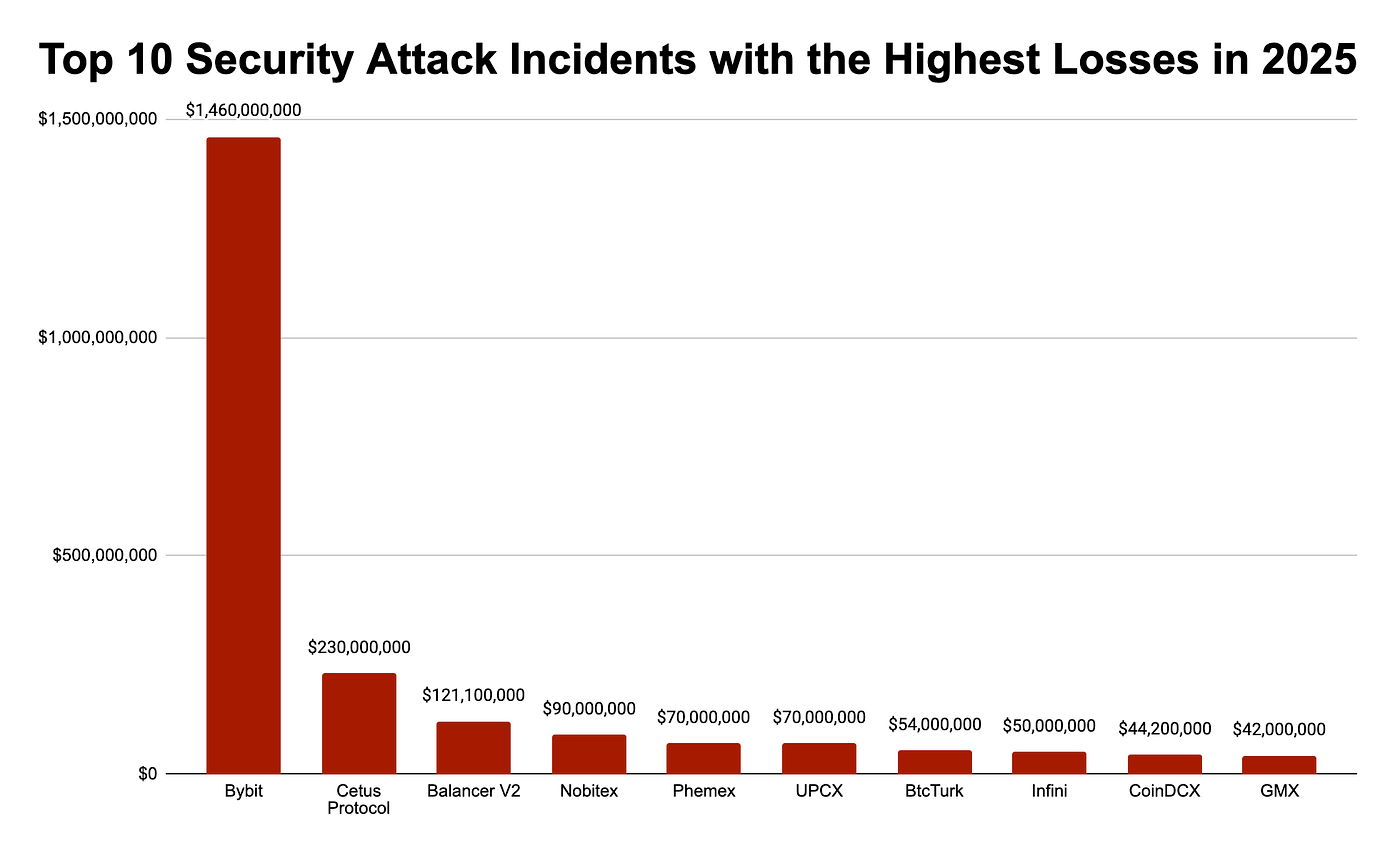
By project segment, DeFi remains the most frequently targeted sector: in 2025, there were a total of 126 security incidents, accounting for approximately 63% of the year’s total, resulting in losses of about USD 649 million — a decrease of roughly 37% compared to 2024 (339 incidents, USD 1.029 billion in losses). Exchange-related incidents numbered only 12 but caused staggering losses of up to USD 1.809 billion, with a single Bybit incident alone accounting for approximately USD 1.46 billion, making it the most severe event of the year.
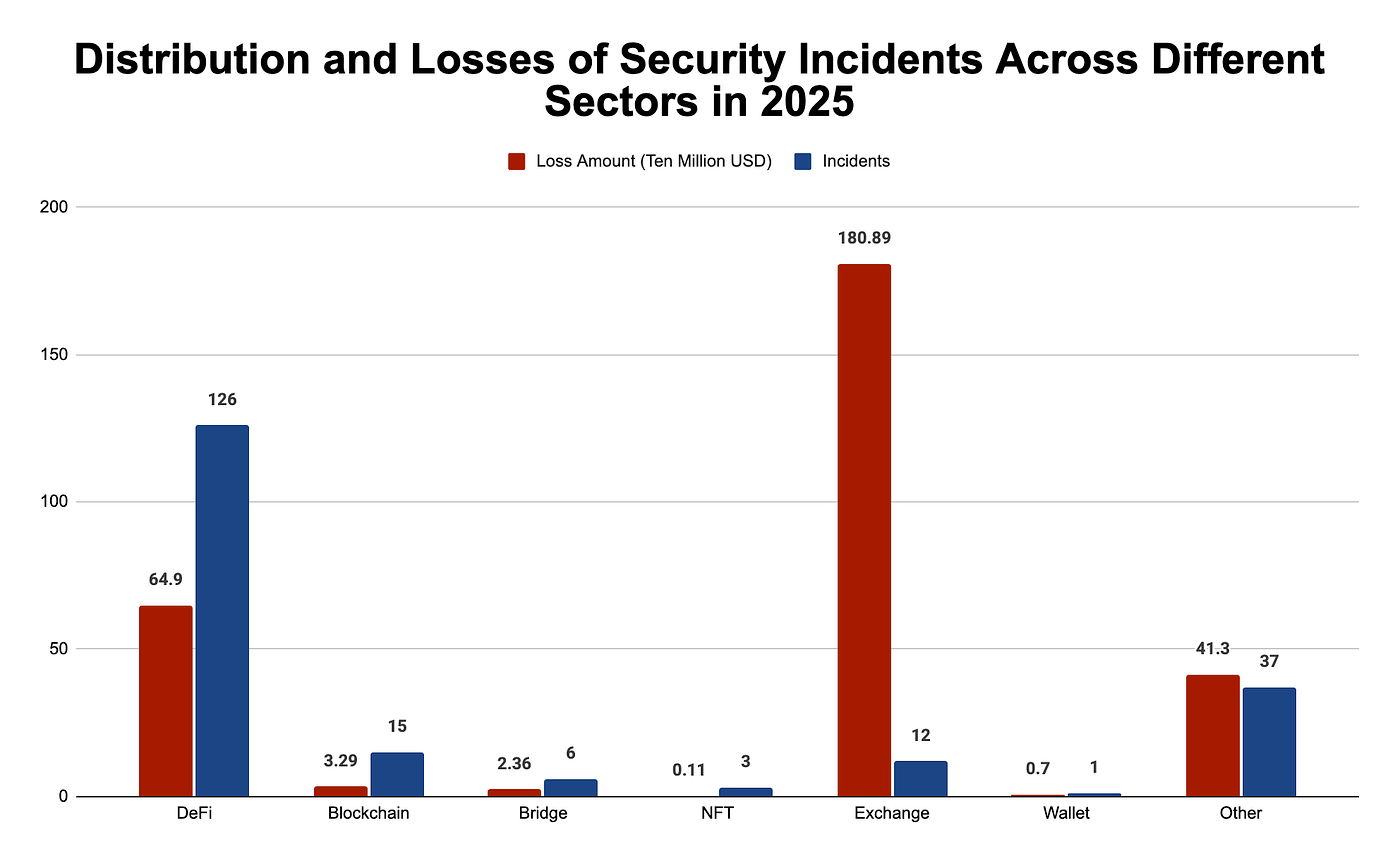
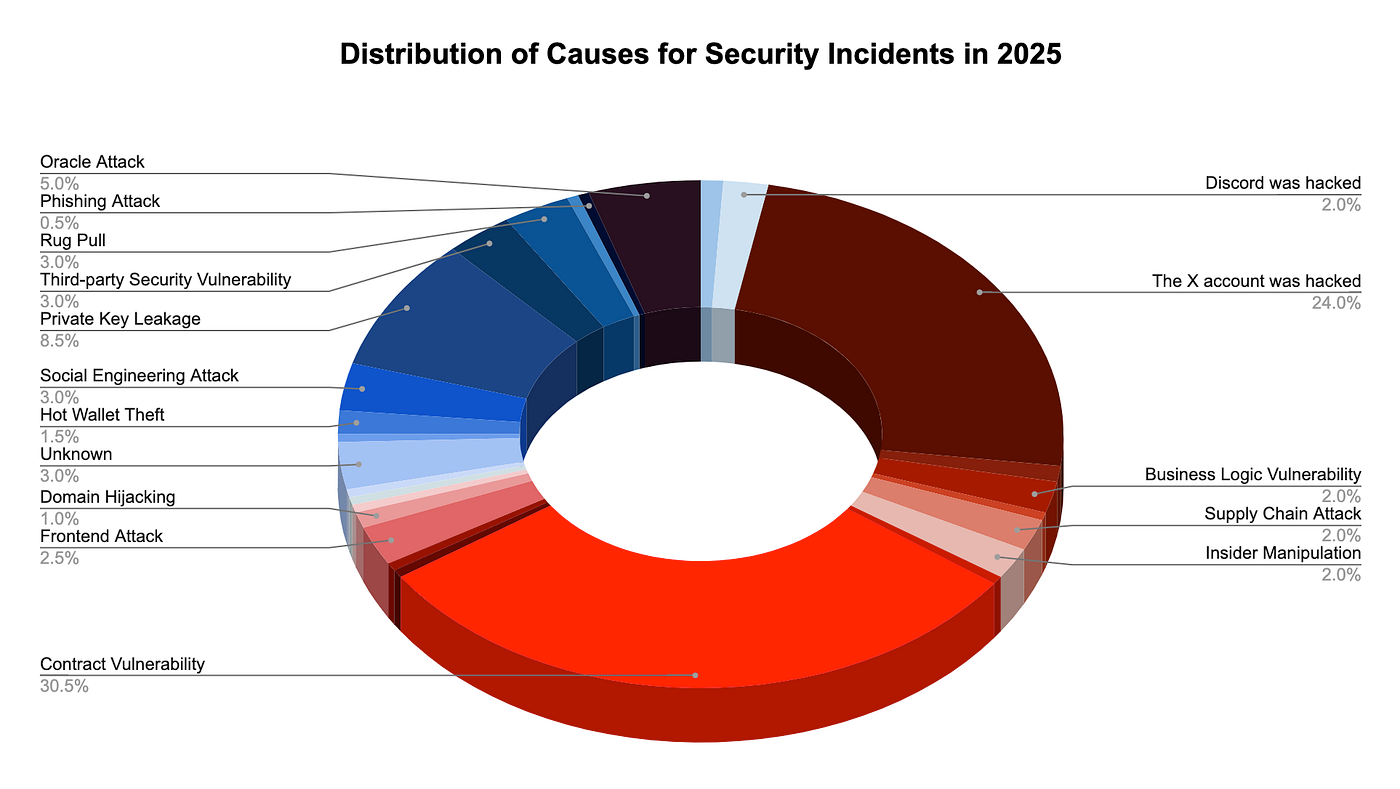
In terms of attack causes, contract vulnerabilities were the primary trigger, accounting for 61 incidents, followed closely by compromised accounts, which accounted for 48 incidents.
Typical Attack Incidents
This section highlights the top 10 security attack incidents by loss in 2025. For full details, please refer to the PDF file at the end.
Scam Techniques
Below are several typical, emerging fraud techniques that deserve close attention in 2025.
Phishing Attacks
In 2025, phishing remained one of the most active risk vectors, and its techniques have evolved far beyond traditional fake websites and counterfeit authorization pages. Attackers now combine system commands, wallet permissions, protocol mechanics, and even device control to execute compound attacks. Instead of simply asking users to reveal their mnemonic phrases, modern phishing methods increasingly rely on guided operations, tricking users into unknowingly completing the transfer of their own assets. These attacks are more covert, more deceptive, and significantly broaden the scope of victims.
This subsection focuses on four representative phishing patterns: ClickFix phishing attacks, Solana wallet Owner‑permission tampering, EIP‑7702 authorization abuse, and the Fake Safeguard Scam.
Social Engineering Attack
In 2025, social engineering attacks showed a clear upward trend in blockchain‑related incidents, increasingly becoming the critical entry point connecting phishing, malware deployment, and asset theft. These attacks center on manipulating trust, using identity impersonation, emotional pressure, and information asymmetry to guide victims into actively cooperating with high‑risk actions. Rather than immediately stealing assets, attackers often conduct multiple rounds of interaction to gradually build credibility, ultimately inducing victims to download malicious software, disclose private keys, or transfer funds to attacker‑controlled addresses.
This subsection analyzes three representative types of social engineering attacks, including fake job‑interview scams, impersonation of “security experts” providing guidance, and counterfeit hardware wallets.
Supply Chain and Open‑Source Ecosystem Poisoning
In 2025, software supply‑chain attacks remained highly active within the blockchain security landscape. Attackers no longer focus solely on compromising well‑known libraries or core infrastructure, but increasingly target open‑source projects, developer tools, and dependency distribution chains. By injecting malicious code, they achieve indirect and large‑scale attacks against downstream users.
These attacks typically do not aim at a single victim; instead, they spread through trusted software components, making their impact broad, difficult to trace, and highly capable of compounding with social‑engineering tactics. This subsection provides a detailed analysis of several recurring poisoning incidents observed in 2025.
Malicious Browser Extensions and Extension Ecosystem Risks
Browser extensions are ubiquitous in Web3 use cases. Whether they are wallet plugins, proxy tools, security-assist extensions, or productivity tools commonly used by developers, these extensions generally possess high permissions, run in the background, and support automatic updates. Once compromised or maliciously exploited, they can stealthily steal data from users and, in some cases, directly cause asset loss. This subsection summarizes the security risks of browser extensions in Web3 scenarios and provides analysis based on representative cases.
Attacks Using AI Technology
With the accelerated adoption of generative AI over the past two years, attackers have begun incorporating it into fraud and attack chains. Compared to traditional tools, AI’s capabilities in text, voice synthesis, image, and video generation significantly reduce the cost of scams. Attacks no longer rely on crude scripts or overtly suspicious behavior; instead, they use highly realistic content, coherent interactions, and precise targeting, making it psychologically much harder for victims to recognize risks. This subsection summarizes the risks of generative AI being abused in cryptocurrency and enterprise security scenarios.
Ponzi Scheme Fraud
In 2025, Ponzi schemes remained one of the most pervasive forms of digital asset fraud. Unlike traditional Ponzi models, the new generation of projects tends to disguise themselves with labels such as “blockchain finance,” “big data technology,” or “international trading platforms,” rapidly expanding through hierarchical commission structures. This subsection summarizes a typical digital asset Ponzi case in 2025 — the operation model and risk characteristics of Xinkangjia DGCX.
III. Anti-Money Laundering Trends
This section primarily covers three areas: anti‑money laundering and regulatory dynamics, fund freezing/recovery data, and cybercrime organizations and the underground network ecosystem.
AML and Regulatory Dynamics
LE and Sanctions Actions
In 2025, law enforcement and sanction actions in the global crypto‑asset sector significantly escalated. Regulatory and enforcement agencies worldwide moved beyond merely issuing policies or compliance guidelines, directly intervening in key areas such as crypto money laundering, fraud, sanction evasion, and illegal financing through asset freezes, entity sanctions, criminal prosecutions, and cross‑border joint operations. Enforcement coverage continued to penetrate deeper, encompassing exchanges, infrastructure service providers, and even individual on‑chain addresses.
This subsection highlights 2025 enforcement dynamics across four areas: combating malware, darknet activities, and cybercrime infrastructure; key regulation and criminal accountability of the crypto exchange Garantex; joint operations targeting fraud, Ponzi schemes, and “pig-butchering” criminal networks; and penalty cases for non‑compliance and illegal operations in crypto services.
Regulatory Policies
In 2025, global crypto‑asset regulation entered a stage of structured and systematic advancement. Policies in various countries gradually transitioned from the previous “exploratory regulation” to “clear rule implementation and unified framework construction.” Compliance is widely regarded as a prerequisite for the development of the crypto market, with high‑frequency policy focus on tax transparency, AML/KYC, custody security, and information disclosure. This subsection summarizes the regulatory policy developments in 2025 across different countries, with detailed entries available in the appendix PDF at the end.
Freeze / Recover Funds Data
In 2025, Tether froze USDT-ERC20 assets on a total of 576 Ethereum addresses, Circle froze USDC-ERC20 assets on a total of 214 Ethereum addresses.
In 2025, there were 18 incidents in which lost funds could still be recovered or frozen after an attack. In these 18 cases, the total stolen funds amounted to approximately $1.957 billion, of which nearly $387 million were returned or frozen, accounting for 13.2% of the total losses in 2025.
Additionally, with strong support from the SlowMist InMist Lab threat intelligence network, SlowMist assisted clients, partners, and publicly disclosed hacking incidents in freezing or recovering approximately $19.29 million in 2025.
Cybercrime Organizations and the Underground Cyber Ecosystem
DPRK Hackers
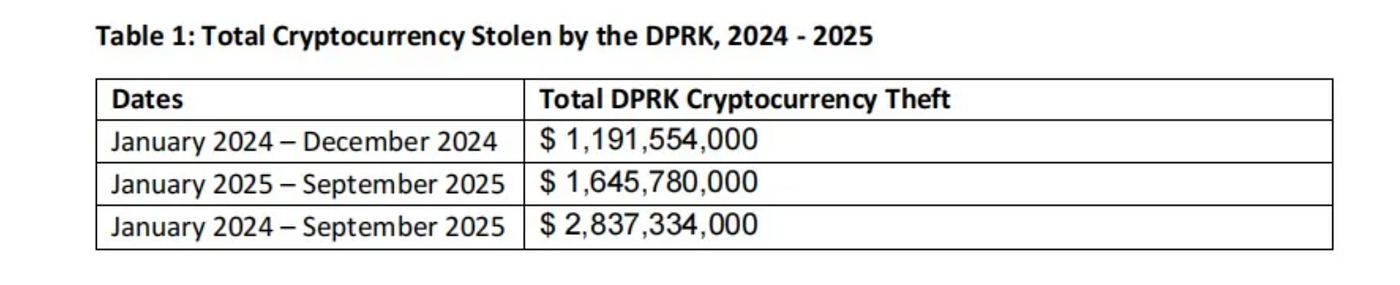
According to a 2025 research report by MSMT, from January 2024 to September 2025, DPRK-related hacker groups attacked cryptocurrency exchanges, wallet service providers, multi-signature infrastructures, and Web3 ecosystem companies worldwide, stealing a total of at least $2.837 billion in crypto assets. Of this amount, approximately $1.645 billion was stolen in just the first nine months of 2025 alone, setting a new historical record.
This subsection summarizes the activity patterns of North Korean hackers in 2025, including their main organizational structure and division of roles, core attack techniques and targeted sectors, as well as the “industrialized workflow” of money laundering and on‑chain fund movement. It further reveals a covert funding‑input model enabled through IT outsourcing and “legitimate employment laundering.”
Drainer
This report analyzes the latest trends in Wallet Drainer phishing attacks across the EVM ecosystem, providing insights for industry practitioners and users to better protect their assets. Special thanks to ScamSniffer for their valuable contribution to this analysis.

- Total losses: $83.85M across 106,106 victims — down 83% and 68% respectively from 2024.
- Largest single theft: $6.5M via Permit signature (September).
- Dominant signature type: Permit remained primary; EIP-7702 malicious signatures emerged after the Pectra upgrade, with 2 large cases in August.
Huione Group
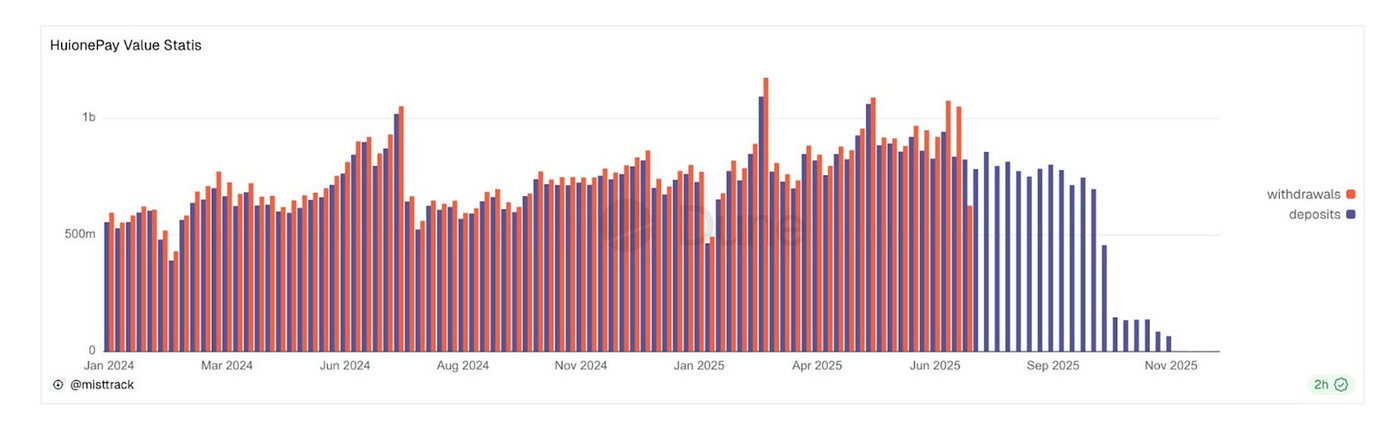
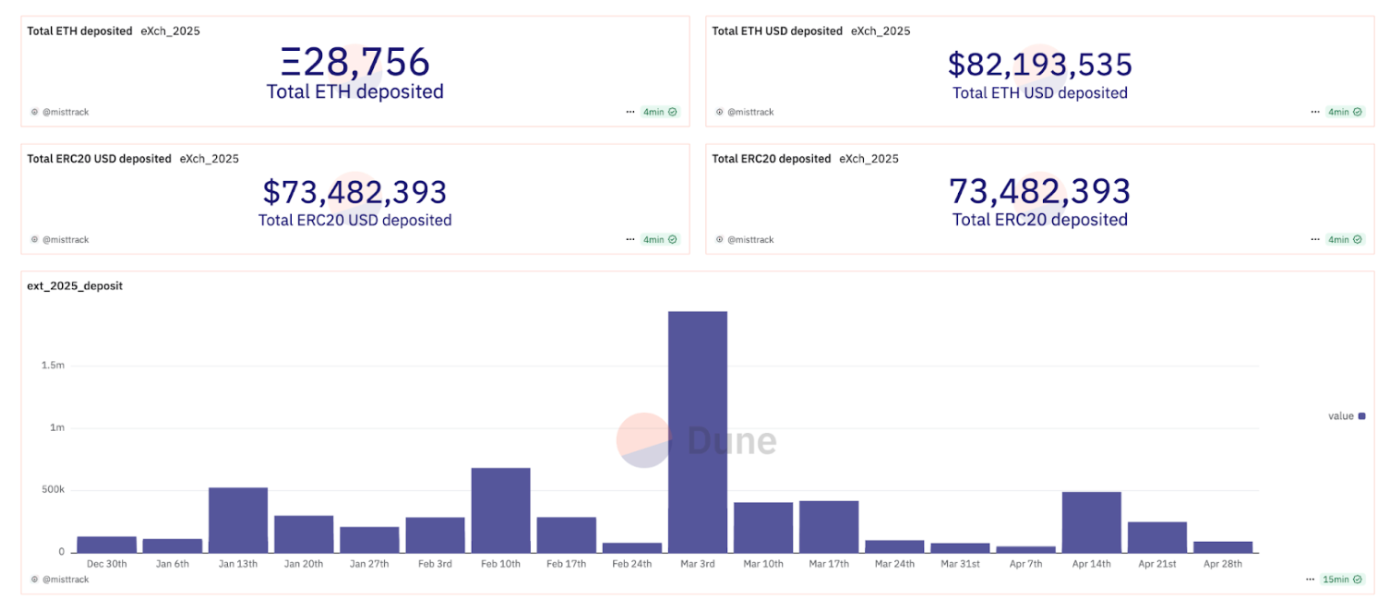
As online scams and cross‑border money‑laundering activities continue to expand in Southeast Asia, platforms represented by Huione Group and its subsidiaries HuionePay and Huione Guarantee have become key targets for global regulators and law enforcement agencies. This subsection outlines the service expansion trajectory of the Huione ecosystem, the current activity of its on‑chain funds, and highlights the cross‑border joint enforcement and regulatory pressures it faces.
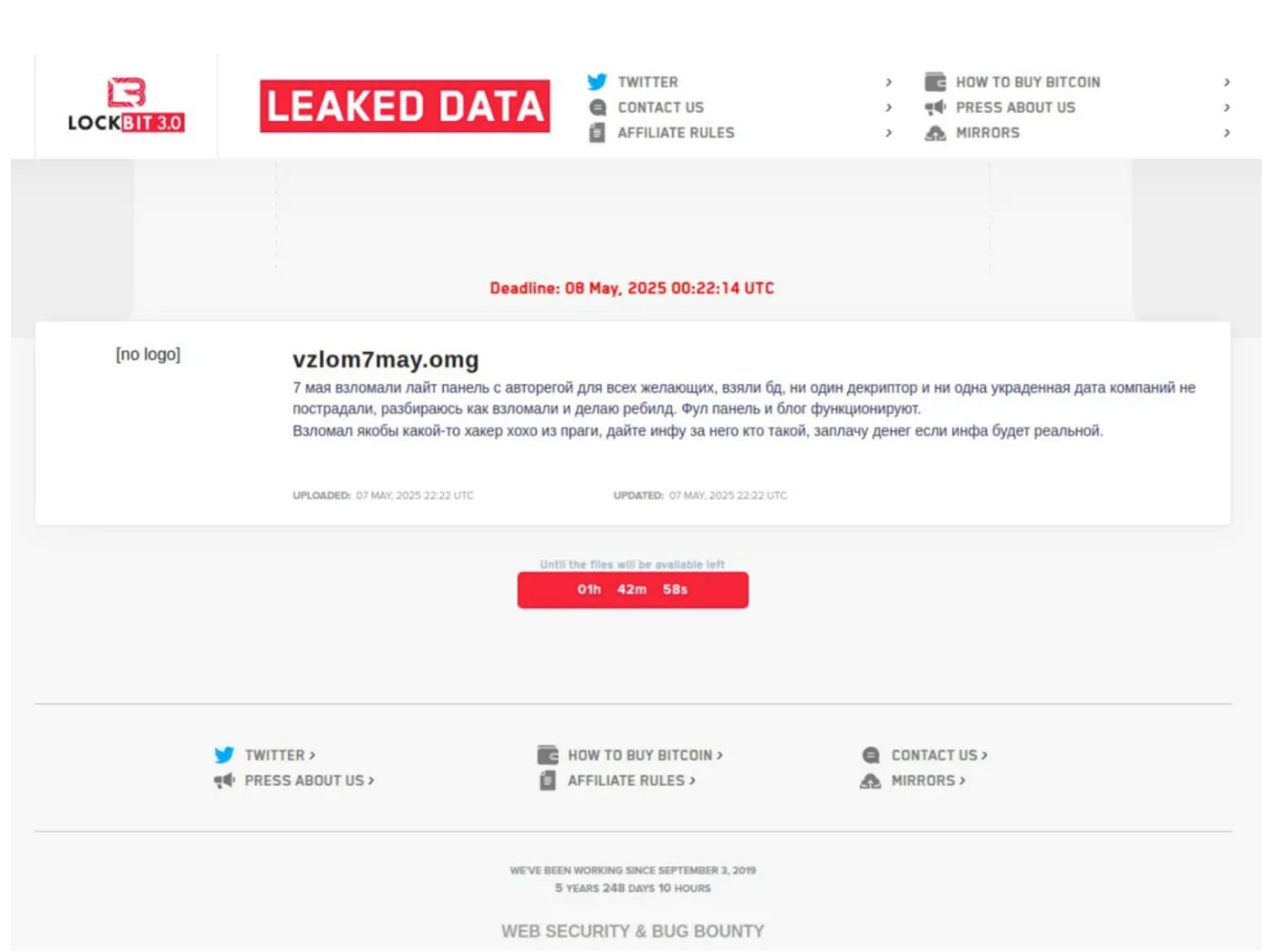
Ransomware / Malware
Ransomware and information‑stealing malware remained major tools for crypto asset theft and illicit profits in 2025. The commercialization of MaaS / RaaS (Malware‑/Ransomware‑as‑a‑Service) further lowered the barrier to entry, enabling many perpetrators with no technical background to launch attacks using turnkey services — fueling a continuously expanding cybercrime supply chain. Over the past year, law enforcement agencies in multiple countries have conducted several major operations targeting core groups. This subsection provides detailed analysis using LockBit and LummaC2 as representative cases.
Privacy / Coin Mixing Tools
In the cryptocurrency money‑laundering ecosystem, privacy protocols and mixing tools have long played a key role.They serve both legitimate users who value privacy and cybercriminal organizations, ransomware groups, and underground laundering networks as important channels to bypass regulation. Based on the analysis of typical regulatory and enforcement cases in 2025, this subsection finds that the line between privacy technologies and illicit abuse is being redefined, with regulatory approaches gradually shifting from “blanket crackdowns” to “distinguishing usage and responsibility.”
IV. Conclusion
Looking back at 2025, the blockchain security and anti‑money laundering ecosystem exhibited three major characteristics: more professionalized attack techniques, increasingly covert criminal networks, and stronger regulatory enforcement. While the number of security incidents stabilized, there were significant structural changes, with persistent risks in permission management, social engineering attacks, and private key leaks. The “service‑oriented” nature of underground tools made plug‑and‑play attacks a reality, extending risks from the technical layer to users and the supply chain.
Money‑laundering networks continued operating around Southeast Asian scams, North Korean attack funds, and privacy/mixing tools. Meanwhile, regulation entered a stage of cross‑border coordinated suppression, with multiple countries simultaneously implementing AML/FATF frameworks, tightening the space for criminals through address seizures, asset freezes, and accountability measures against mixing operators. Security and compliance have shifted from being “added capabilities” to becoming a commercial survival threshold, with the industry’s competitive focus no longer on technical narratives but on who can build a sustainable security and compliance framework.
In line with this trend, SlowMist continues to advance AI-driven security and compliance capabilities. We firmly believe that security should never be understood as a one-off “project audit” or “emergency tracking,” but rather as a comprehensive, integrated closed-loop system covering threat detection and defense before, during, and after incidents. Pre-incident measures include security audits and training; during incidents, they involve on-chain monitoring and real-time hacker activity detection; post-incident measures include tracking, forensics, and emergency response. In practice, SlowMist operationalizes this closed-loop capability through its products and services, including MistEye (a Web3 threat early-warning and dynamic monitoring system based on threat intelligence models), MistTrack (on-chain analysis and AML/KYT compliance tracking platform), InMist Lab (a global threat intelligence collaboration network), as well as offensive/defensive operations and audit services. Powered by AI, these capabilities enable automated, intelligent, and real-time threat identification, tracking, forensics, and compliance support, providing the industry with a robust, long-term security foundation.
V. Disclaimer
The content of this report is based on our understanding of the blockchain industry, data from the SlowMist blockchain hacked archive database SlowMist Hacked, and the anti-money laundering tracking system MistTrack. However, due to the “anonymous” nature of blockchain, we cannot guarantee the absolute accuracy of all data and cannot be held responsible for errors, omissions, or losses caused by using this report. Additionally, this report does not constitute any investment advice or the basis for other analyses. We welcome criticism and corrections for any oversights or inadequacies in this report.
https://www.slowmist.com/report/2025-Blockchain-Security-and-AML-Annual-Report(EN).pdf
About SlowMist
SlowMist is a threat intelligence firm focused on blockchain security, established in January 2018. The firm was started by a team with over ten years of network security experience to become a global force. Our goal is to make the blockchain ecosystem as secure as possible for everyone. We are now a renowned international blockchain security firm that has worked on various well-known projects such as HashKey Exchange, OSL, MEEX, BGE, BTCBOX, Bitget, BHEX.SG, OKX, Binance, HTX, Amber Group, Crypto.com, etc.
SlowMist offers a variety of services that include but are not limited to security audits, threat information, defense deployment, security consultants, and other security-related services. We also offer AML (Anti-money laundering) software, MistEye (Security Monitoring), SlowMist Hacked (Crypto hack archives), FireWall.x (Smart contract firewall) and other SaaS products. We have partnerships with domestic and international firms such as Akamai, BitDefender, RC², TianJi Partners, IPIP, etc. Our extensive work in cryptocurrency crime investigations has been cited by international organizations and government bodies, including the United Nations Security Council and the United Nations Office on Drugs and Crime.
By delivering a comprehensive security solution customized to individual projects, we can identify risks and prevent them from occurring. Our team was able to find and publish several high-risk blockchain security flaws. By doing so, we could spread awareness and raise the security standards in the blockchain ecosystem.



